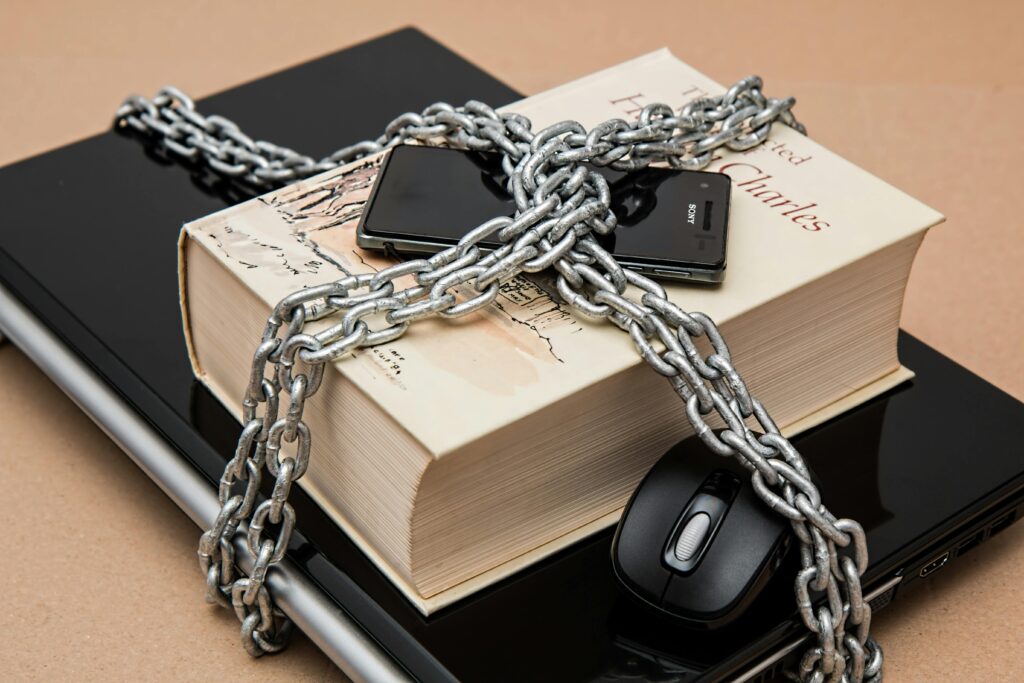
When we think about cybersecurity we usually focus on software like firewalls and antivirus programs.. The truth is, every device connected to your business is a potential entry point for attackers. Cybersecurity is not about systems it is about devices.. In most businesses the most vulnerable devices are not the ones you expect. They are often the ordinary devices, the ones that are overlooked and not protected.
Understanding which devices pose the risk is essential for building a strong security posture. This article explores the vulnerable devices in your business how attackers exploit them and what you can do to secure them.
The Expanding Attack Surface
Modern businesses rely on a lot of devices, including laptops, smartphones, routers, printers and smart devices. Each device connected to your network increases the number of points where an attacker could try to gain access. The challenge is not the number of devices but how they are managed and secured.
The devices connected to your network include:
- Laptops and desktops
- Smartphones and tablets
- Routers and network equipment
- Printers and scanners
- devices
- External storage devices
Each of these devices increases your attack surface, which is the total number of points where an attacker could try to gain access.
1. Employee Laptops: The Primary Target
Laptops are the backbone of business operations and they are one of the most targeted devices.
Employee laptops are vulnerable because they are used both inside and outside networks. They are frequently connected to Wi-Fi, which is not secure. They also store business data and often lack consistent security configurations.
The common risks associated with employee laptops include malware infections from downloads phishing attacks that lead to credential theft and loss or theft of the device itself.
To secure employee laptops you should enable disk encryption, install and maintain endpoint protection software require strong passwords and multi-factor authentication and keep operating systems and applications updated.
Laptops are high-value targets because they combine accessibility with data.
2. Smartphones: The Overlooked Access Point
Smartphones are often treated as devices even when they are used for business purposes.
Smartphones are vulnerable because there is a line between personal and professional use. They also have apps installed and are frequently connected to unsecured networks.
The common risks associated with smartphones include apps that steal data phishing via SMS or messaging apps and unauthorized access to business accounts.
To secure smartphones you should use device lock screens and biometric authentication restrict app installations to trusted sources enable remote wipe capabilities and separate work and personal data where possible.
Ignoring security is one of the fastest ways to create hidden vulnerabilities.
3. Routers and Network Devices: The Silent Gatekeepers
Your router is the hub of your network and it is a critical point of failure.
Routers are vulnerable because default credentials often remain unchanged firmware updates are frequently ignored and there is visibility into suspicious activity.
The common risks associated with routers include access to the network, interception of data traffic and creation of backdoors for persistent access.
To secure routers you should change default usernames and passwords immediately regularly update firmware use encryption and disable remote management unless absolutely necessary.
If a router is compromised it can expose every device.
4. Printers and Multifunction Devices: The Hidden Risk
Printers are rarely considered a security threat. They are network-connected computers with storage capabilities.
Printers are vulnerable because they often lack security configurations store copies of printed documents and are rarely monitored or updated.
The common risks associated with printers include access to sensitive documents use as an entry point into the network and data leakage through stored print jobs.
To secure printers you should change default credentials restrict network access to users regularly clear stored data and update firmware when available.
Printers are an example of a device that is ignored until it becomes a problem.
5. IoT Devices: Convenience vs. Security
Smart devices, such as cameras and smart TVs are increasingly common in workplaces.
IoT devices are vulnerable because they are designed for convenience, not security. They have default settings and limited update mechanisms.
The common risks associated with IoT devices include surveillance, use in botnets for large-scale attacks and network infiltration through weak points.
To secure devices you should change default settings and credentials place IoT devices on a separate network disable unnecessary features and keep firmware updated when possible.
IoT devices often expand your attack surface without adding security.
6. External Storage Devices: The Physical Threat
USB drives and external hard drives are widely used for data transfer and backups.
External storage devices are vulnerable because they are easily lost or stolen can carry malware between systems and often lack encryption.
The common risks associated with storage devices include data breaches from lost devices, malware infections from unknown sources and unauthorized data copying.
To secure storage devices you should encrypt all external storage devices restrict use of unknown USB drives and implement policies for handling sensitive data.
Physical devices can bypass defenses entirely.
7. Legacy Systems: The Forgotten Weak Link
Older devices and systems often remain in use because they still work.
Legacy systems are vulnerable because they no longer receive security updates are incompatible with protections and are difficult to monitor or integrate.
The common risks associated with legacy systems include exploitation of known vulnerabilities inability to detect or respond to threats and compatibility issues that create security gaps.
To secure legacy systems you should replace systems whenever possible isolate them from critical networks and limit their functionality to essential tasks.
Legacy devices are targets for attackers.
8. Shared Workstations: The Accountability Problem
In some environments multiple employees use the device.
Shared workstations are vulnerable because there is a lack of accountability shared credentials or sessions and inconsistent usage practices.
The common risks associated with shared workstations include access to data, difficulty tracing incidents and increased likelihood of human error.
To secure workstations you should require individual user accounts enforce automatic logouts and monitor usage activity.
Shared devices blur. Increase risk.
9. Personal Devices (BYOD): The Blurred Boundary
Bring Your Device (BYOD) policies are common especially in small businesses.
Personal devices are vulnerable because there is a lack of control, mixed personal and business usage and variable security standards.
The common risks associated with devices include data leakage, inconsistent security practices and exposure to personal app vulnerabilities.
To secure devices you should establish clear BYOD policies require basic security measures and limit access to sensitive systems.
Convenience often comes at the cost of control.
10. Backup Systems: The Line of Defense
Backup devices are critical but often overlooked in security planning.
Backup systems are vulnerable because they are connected to the network as primary systems not regularly tested or secured and assumed to be safe by default.
The common risks associated with systems include ransomware encrypting backup data, data corruption or loss and unauthorized access to stored information.
To secure backup systems you should store backups in secure locations use offline or cloud-based backup solutions and test recovery processes regularly.
A compromised backup system removes your safety net.
The Common Pattern: Neglect, Not Complexity
What makes these devices vulnerable is not their limitations it is how they are managed.
The common themes include default settings left unchanged lack of updates and maintenance minimal monitoring and assumptions that low-risk devices do not need protection.
Attackers exploit these gaps because they are predictable.
Building a Device Security Strategy
You do not need tools to improve device security. Focus on consistency and visibility.
The key principles include:
- Inventory Your Devices: Know what is connected to your network
- Standardize Security Measures: Apply protections across all devices
- Limit Access: Only allow what is necessary
- Keep Everything Updated: Regular maintenance is
- Monitor Activity: Look for behavior
- Educate Users: Human behavior impacts device security
Common Mistakes to Avoid
You should avoid treating computers as security risks ignoring secondary devices like printers and routers delaying updates and maintenance allowing uncontrolled use of personal devices and assuming small businesses are not targets.
Avoiding these mistakes can significantly reduce your risk.
Final Thoughts
The vulnerable devices in your business are not necessarily the most advanced or the most valuable they are the ones that are overlooked.
Cybersecurity is not about protecting a system it is, about understanding how every device contributes to your overall risk.
By identifying and securing these points you transform your business from an easy target into a more resilient operation.
In the end attackers do not need to break through your defenses if they can find a weak device somewhere else.
Your job is to make sure there are no options.
That starts with knowing where your real vulnerabilities lie.
